Traditional networks use to function in a very intrinsic security mechanism wherein a person, third application, or any sort of application could’ve verified and subsequently be trusted. Well, it won’t be difficult to say that this has caused many security breaches and incalculable losses. Trust for access control placed simply on the basis of verification has resulted in many losses and security threats.
As per a report by the FBI Internet Crime Complaint Center, a massive amount of $26.2 billion was the total domestic and international losses incurred all over the world between 2016-2019 due to weak cybersecurity access control. So many loose ends in granting verification and trust are the reason why attackers have made it easier to break into the networks and systems.
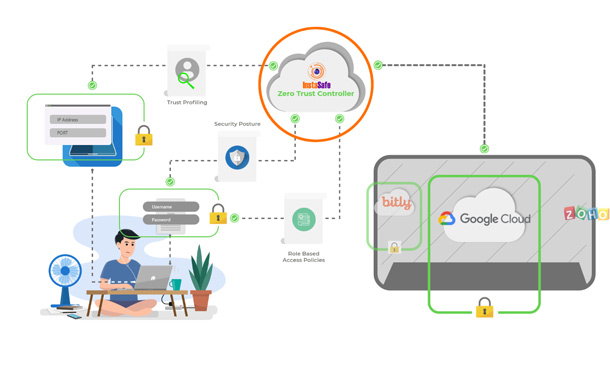
Here is where Identity-centric security like zero trust security and software-defined perimeter comes into the mainstream. Responding to today’s dangerous and dynamic security threat landscape, these identity-centric security systems and software-defined perimeter products strive to set effective and practical standards for evaluating security in cloud infrastructures, remote frameworks and security for web access.
Basically, the identity-centric zero-trust and software-defined perimeter stand by 3 simple core principles:
- Make sure to always verify.
- Never trust anybody.
- Be hyperactive to protect everything, everywhere, and at every time
What is a Software-Defined Perimeter (SDP)?
Software-Defined Perimeter is the best way to limit and restrict access control for networks and offer customized, managed, and secure access within the networks. It goes by the principle of verifying each and every device and its identity intensively before granting access to the same.
Through SDP, the IT team and security managers can deploy security gateways over the cloud infrastructure or on-premise to secure the remote access of employees. The IT team and managers can keep a good eye on who is getting access and how is the sensitive data managed properly under the organizational networks. SDP has proved to be very effective against threats like DDOS, Man-in-the-middle, OWASP10, and many advanced persistent security threats.
How is software-defined perimeter effective in protecting networks?
- Flexible – Deploying SDP, you can facilitate automated security activities that will direct automatically which devices are allowed access and which users and identities are verified to access the networks.
- Accurate segmentation – SDP promotes precise segmentation by integrating with identity providers, SAML services, and any active directories.
- Worldwide access – With the help of SDP, you can easily facilitate unified gateways that are secured and evaluate access to all the resources from any location. This promotes convenient and secured remote access for the users accessing from different locations all the while verifying with the highest level of security.
- Utmost secured and encrypted – SDP ensures to maintain a strong layer of client-end protection that takes care of robust privacy measures and data classification. It takes utmost care of evaluating identity access while encrypting the whole network traffic with effective mutual TLS encryption. It also manages security effectively on the OS and application level.
Some key Software-Defined Perimeter product attributes
- The Software-Defined Networking (SDN) – SDN works intensively in abstracting layer 2 networking. Layer 2 network refers to operating of the lower lever infrastructures, that facilitates connections, communications, and where the packets are needed to be sent. It acts as a very important function for all public cloud services and infrastructure. The SDN helps the service provider to centralize all the switching and routing functions and gives the ability to manage security for millions of logically isolated networks.
- The Hypervisors – Hypervisors are the core operating systems that manage and run virtual machines. It is basically managed on the physical machine but distributes the hardware resources to multiple virtual machines. The hypervisors have completely been a revolution in how server deployment is carried on today securely and how IT services are delivered effectively. These hypervisors run virtual machines like ESXi, Microsoft Hyper-V, VMWare, etc.
- The Network Function Virtualization (NFV) – NFV offers support in services like load balancing, firewalls, accelerators, IDS, and CDNs by building upon SDN. These facilitate quick and easy deployment of security configurations. NFV is very effective and convenient in deploying configurations securely without going much into complications.
Why are businesses moving more towards Software-Defined Perimeter?
Increased engagements on cloud-based infrastructure and remote workforce access have led to the need for major policy-based security architecture. Businesses have understood the importance of employing security mechanisms like zero-trust security, multi-factor authentication, and software-defined perimeter.
As per the forecasts from MarketsandMarkets, the market size for the deployment of software-defined perimeter among the businesses worldwide is expected to grow to $13.8 billion by 2024. Almost a 36.5% CAGR growth. This is because –
- Best replacement to VPN connection, NACs, and Firewalls
Identity-centric systems with software-defined perimeters offer a robust security framework against the bare minimum security standards of general VPNs, NACs, and firewalls.
- Secured Policy-based access
Through SDP, precise segmentation of one-to-one network connections between the end-user and the resources is optimized securely. Everything other than that gets invisible and unapproachable. It works effectively in hiding network resources from unwanted traffic and unauthorized users that ultimately trims down the attack battlefield. This promotes the least privilege and authorized access to the network.
- Automatic gateways deployment
The traditional hardware installations and tedious hours of constant support can be replaced effectively with the automated deployments of gateways in any location. This trims down a hell lot of costs and manages IT security more efficiently. It promotes simplified and more effective security and network management.
Final Words
The Identity-centric systems and software-defined perimeter can play a huge role in the times where a massive transition to cloud-based and more remote working is on the roll. It can promote more secure and efficient identity verification and resource access. It lays down strong standards to govern verification of the users, networks, applications, and devices accessing through the network. With more and more businesses moving towards security mechanisms like zero-trust security, microsegmentation, and software-defined perimeter, cybersecurity threats can be managed and controlled to a major extent.
SDP based companies like Instasafe and Sophos strive to offer you the most powerful and robust security tools and mechanisms that will safeguard your remote and cloud-based systems against the highest of potential threats. Browse on through our website and connect with us today to get hold of some of the most secured interfaces you would ever come across.